If you're juggling remote endpoints, hybrid teams, and looming audits, you know that compliance isn’t just a checkbox. It’s the foundation of trust, eligibility for contracts, and—frankly—keeping your job. NIST compliance is more than just a federal nicety. It’s your north security standard star for building a cybersecurity program that can take a hit and keep running.
This guide cuts through the noise and gives you a no-fluff roadmap to understanding, achieving, and maintaining NIST compliance.
Key takeaways
- NIST compliance is essential for organizations managing sensitive data, particularly those working with the U.S. government, as it enhances cybersecurity and risk management.
- Achieving NIST compliance involves conducting risk assessments, developing compliance plans, and implementing security controls tailored to identified vulnerabilities and create incident response plans.
- Ongoing monitoring and maintenance of NIST compliance are critical, requiring regular audits, employee training, and compliance tools to adapt to evolving cyberattacks.
What is the NIST standard?
The National Institute of Standards and Technology (NIST) is part of the U.S. Department of Commerce and the gold standard when it comes to cybersecurity frameworks. NIST compliance means aligning your organization with their guidelines—especially the NIST Cybersecurity Framework (CSF), NIST SP 800-53, or NIST SP 800-171.
These frameworks help you:
- Identify and manage cybersecurity risks
- Align your security strategy with business needs
- Prepare for other frameworks (like FedRAMP, FISMA, CMMC, or ISO 27001)
These frameworks align with various cybersecurity standards, providing a comprehensive method to address vulnerabilities and enhance data security across industries. The guidelines are dynamic and evolve over time, ensuring that organizations can systematically tackle emerging threats while maintaining robust security measures.
Achieving NIST compliance demands ongoing commitment and continuous evaluation. This perpetual process ensures that organizations stay ahead of new cybersecurity challenges and maintain a resilient security posture.
Why NIST compliance matters
Compliance with NIST guidelines significantly enhances an organization’s security posture, leading to improved data security and risk management. Following these guidelines helps organizations create a safer environment for sensitive data, crucial for maintaining trust with customers and partners. Aligning cybersecurity strategies with NIST not only supports overall business objectives but also ensures that security measures are robust and effective.
Who needs to be NIST compliant? Any organization working with the federal government, DoD contracts, or government agencies must comply—especially if handling Controlled Unclassified Information (CUI). But even if you're not federally mandated, adopting NIST practices boosts your security maturity and audit readiness.
Meet the big three: Core NIST frameworks
The NIST security standards are comprehensive guidelines designed to manage cybersecurity risks effectively. Some of the most commonly used standards include the NIST Cybersecurity Framework ( NIST CSF), NIST SP 800-53, and NIST SP 800-171. These frameworks provide detailed instructions on safeguarding sensitive information and are applicable to both government and private organizations handling such data.
NIST CSF
A high-level framework built around five pillars: Identify, Protect, Detect, Respond, and Recover. Great for mapping your overall strategy and aligning IT with leadership. It is designed to improve the security posture of information systems, particularly within federal agencies, providing a structured approach to addressing and managing cybersecurity threats
NIST 800-53
NIST SP 800-53 is particularly notable for its extensive set of controls aimed at protecting sensitive information against various threats. It includes over 1,000 security controls organized into five core areas, ensuring a robust security framework. This standard is vital for organizations looking to enhance their security posture and effectively protect confidential information.
NIST 800-171
NIST SP 800-171, on the other hand, focuses on protecting Controlled Unclassified Information (CUI) in non-federal systems. This standard is crucial for organizations that need to comply with defense contract requirements, ensuring that sensitive information is adequately protected.
Planning for CMMC? You’re already halfway there if you’re aligned with 800-171.
Core principles of the NIST cybersecurity framework (CSF)
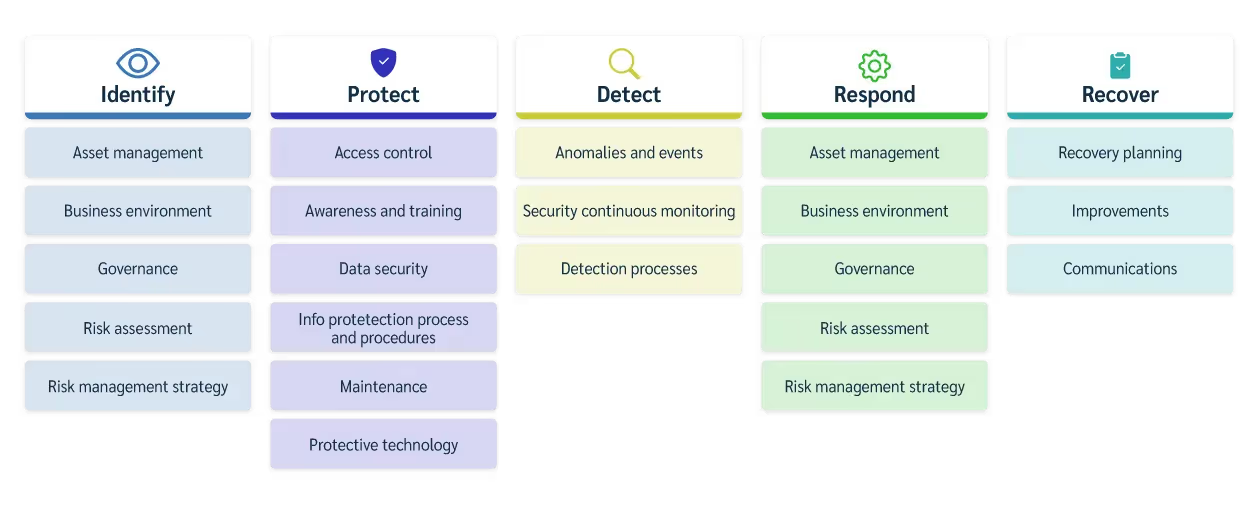
The NIST Cybersecurity Framework consists of five core functions:
- Identify
- Protect
- Detect
- Respond
- Recover
These functions form the backbone of a robust cybersecurity strategy, helping organizations manage cybersecurity risks effectively.
The Identify Function helps in understanding and managing cybersecurity risks related to systems, assets, and people. It involves identifying critical assets and vulnerabilities, enabling organizations to prioritize their security efforts.
The Protect Function involves implementing safeguards to ensure delivery of critical services and mitigating potential cybersecurity events. Establishing strong security controls helps protect data from unauthorized access and breaches.
The Detect Function allows organizations to promptly identify cybersecurity events and evaluate their impacts, crucial for early threat detection and response, minimizing damage.
The Respond Function involves containing the impact of cybersecurity incidents and managing communication during events. Effective response strategies help mitigate effects and restore normal operations swiftly.
The Recover Function outlines actions to restore capabilities and services compromised during a cybersecurity incident, ensuring organizations can quickly return to normal operations.
Your roadmap to NIST compliance
Achieving NIST compliance involves several critical steps, including conducting a risk assessment, developing a compliance plan, and implementing security controls. Each of these steps plays a vital role in building a robust cybersecurity framework that aligns with NIST guidelines.
Conducting a risk assessment
A thorough risk assessment forms the foundation of an effective cybersecurity strategy. It involves evaluating the effectiveness of current controls against potential vulnerabilities, aiding in prioritizing cybersecurity efforts. Understanding their weaknesses allows organizations to focus resources on critical areas, ensuring a robust security posture through risk assessments.
Evaluate your current environment by answering these questions:
- What sensitive data are you handling?
- Where are your vulnerabilities and potential cyber threats?
- What are your most critical assets?
The Identify Function of the NIST Cybersecurity Framework is crucial in this process. Identifying critical assets, vulnerabilities, and potential threats helps organizations develop a comprehensive understanding of their cybersecurity risks, essential for implementing targeted security measures.
CISO Tip: Don’t skip data classification. You can’t protect what you can’t define.
Developing a compliance plan
This is your blueprint for implementation. This cross-functional compliance document should include:
- Defining cybersecurity management team. Having a dedicated team ensures that cybersecurity strategies are cohesive and well-coordinated.
- Categorize data to determine appropriate security measures based on sensitivity levels.
- Assign budget and resources. This ensures that security measures are appropriately prioritized and funded, leading to more effective risk management.
Implementing security controls
Implementing security controls is a critical step in achieving NIST compliance. Let’s start with foundational controls:
- Access control management (least privilege)
- Multi-factor authentication
- Encryption at rest and in transit
- Endpoint monitoring and patching
These controls should address vulnerabilities identified in the risk assessment, ensuring effective data protection. A tailored approach to security controls is crucial for effectively mitigating identified risks. Focusing on specific vulnerabilities allows organizations to implement targeted measures that provide the highest level of protection.
Monitoring and maintaining compliance
NIST compliance is not a “set-it-and-forget-it” deal. Monitoring and maintaining compliance is an ongoing process requiring continuous effort. Adopting the NIST CSF helps businesses adapt to evolving regulations and compliance demands. Regular security training for employees is crucial to enhance awareness of their cybersecurity roles.
Continuous monitoring tools are essential for detecting potential breaches and anomalies in real-time, helping organizations spot unusual activities and potential threats for prompt response and mitigation. Maintaining detailed documentation of policies, controls, and response plans is necessary for streamlining compliance audits.
Overcoming common challenges
Achieving NIST compliance is not without its challenges:
- Resource constraints: Resource and budget limitations present a significant hurdle for many organizations. Use automation platforms (Sprinto, Drata) and outsource to MSSPs if needed.
- Staff pushback: Resistance from staff may arise due to fears of disruption or increased workload when implementing NIST guidelines. Communicate benefits in terms of reduced risk, smoother audits, and fewer breaches.
- Complexity: NIST compliance requirements can lead to confusion, making it difficult for organizations to fully understand their obligations. Start with CSF as a baseline, then scale up to 800-171 or 800-53 based on scope.
Leveraging tools and resources for compliance
NIST offers various materials, including Quick Start Guides and framework profiles, to help organizations implement its guidelines effectively. Numerous tools and platforms are available to assist with compliance efforts. Your compliance tech stack should Include:
- SIEM (e.g., Splunk, Microsoft Sentinel)
- EDR/XDR (e.g., CrowdStrike, SentinelOne)
- Vulnerability Scanners (e.g., Tenable, Qualys)
- Compliance Automation Tools (e.g., Sprinto, Drata)
- Remote Asset Management (e.g., Prey, Miradore)
Want to use Prey?, learn how Prey can help you with NIST CSF.
Benefits of being NIST compliant
Being NIST compliant offers numerous benefits, including enhanced data security and improved overall security posture. Compliance with NIST guidelines is essential for protecting sensitive information and maintaining stakeholder trust. Organizations that achieve NIST compliance are often regarded as more trustworthy by clients and partners.
NIST compliance is also beneficial for businesses seeking government contracts and partnerships. By adhering to NIST standards, organizations can improve their chances in contract bids and establish robust risk management practices.
TL;DR: NIST isn’t just about meeting requirements. It’s about building a security culture that’s resilient, audit-ready, and business-aligned.
Summary
In conclusion, mastering NIST compliance is a journey that requires dedication, continuous improvement, and leveraging available resources. By understanding the importance of NIST compliance, implementing key security standards, and overcoming common challenges, organizations can enhance their security posture and build trust with stakeholders. Prioritize cybersecurity and make NIST standard a cornerstone of your organization’s strategy.
Frequently asked questions
What is NIST compliance?
It means aligning your organization with NIST’s cybersecurity guidelines to manage risk, protect sensitive data, and—if applicable—qualify for government contracts.
Why is NIST compliance important for businesses?
NIST compliance is essential for businesses as it strengthens security measures and improves risk management, particularly for those looking to collaborate with the U.S. government. Adhering to these standards not only protects sensitive information but also fosters credibility and trust with stakeholders.
What are the key NIST security standards?
NIST Cybersecurity Framework (CSF), NIST SP 800-53, and NIST SP 800-171, all aimed at effectively managing cybersecurity risks and safeguarding sensitive information.
What are the core principles of the NIST Cybersecurity Framework?
The core principles of the NIST Cybersecurity Framework are encapsulated in its five functions: Identify, Protect, Detect, Respond, and Recover. These functions guide organizations in effectively managing cybersecurity risks.
How do I get started?
Start with a risk assessment and use CSF to build a structured approach. Use automation where possible, and never underestimate the power of good documentation.
Is NIST just for government contractors?
Nope. Even private companies use NIST as their foundation to prepare for frameworks like ISO 27001 or SOC 2.
How can organizations overcome challenges in achieving NIST compliance?
To overcome challenges in achieving NIST compliance, organizations should prioritize clear communication, provide adequate training, leverage available resources, and allocate sufficient budget and staff for cybersecurity initiatives. This strategic approach enhances overall compliance efforts and effectiveness.





